Basic Routing on Multilayer Switch - Connected Network - No VLAN
Basic Routing on Multilayer Switch 2 - Connected Network - No VLAN
We keep 3 networks and do intervlan routing with Multilayer switch as below:
 |
| Topology |
Keep the following picture as a reference while reading the info for better understanding.
 |
| Reference Topology |
Task Breakup
- Configure IP Addresses of Laptops
- Create VLANs on Switch
- Assign VLANs to Interfaces on Switch
- Configure IP Addresses to VLAN on Switch
- View VLAN Information
- Enabling Routing
- Validation
- Alternate Topology
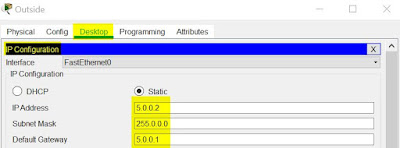
| PC Name | IP Address | Subnet Mask | Default Gateway |
| Inside1-1 | 172.16.0.11 | 255.255.0.0 | 172.16.0.1 |
| Inside1-2 | 172.16.0.12 | 255.255.0.0 | 172.16.0.1 |
| Inside2-1 | 10.0.0.11 | 255.0.0.0 | 10.0.0.1 |
| Inside2-2 | 10.0.0.12 | 255.0.0.0 | 10.0.0.1 |
| Outside | 5.0.0.11 | 255.0.0.0 | 5.0.0.1 |
2. Create VLANs on Switch
As a good convention, we create VLANs and assign names to them
As a good convention, we create VLANs and assign names to them
routing(config)#vlan 172 routing(config-vlan)#name vlan-172 routing(config-vlan)#exit routing(config)#vlan 10 routing(config-vlan)#name vlan-10 routing(config-vlan)#exit routing(config)#vlan 5 routing(config-vlan)#name vlan-5 routing(config-vlan)#exit
3. Assign VLANs to Interfaces on Switch
| PC Name | IP Address | Subnet Mask | Default Gateway | Switchport interface | VLAN ID |
| Inside1-1 | 172.16.0.11 | 255.255.0.0 | 172.16.0.1 | gig 1/0/1 | VLAN 172 |
| Inside1-2 | 172.16.0.12 | 255.255.0.0 | 172.16.0.1 | gig 1/0/2 | VLAN 172 |
| Inside2-1 | 10.0.0.11 | 255.0.0.0 | 10.0.0.1 | gig 1/0/11 | VLAN 10 |
| Inside2-2 | 10.0.0.12 | 255.0.0.0 | 10.0.0.1 | gig 1/0/12 | VLAN 10 |
| Outside | 5.0.0.11 | 255.0.0.0 | 5.0.0.1 | gig 1/0/5 | VLAN 5 |
routing(config)#int gig 1/0/1 routing(config-if)#switchport mode access routing(config-if)#switchport access vlan 172 routing(config-if)#exit routing(config)#int gig 1/0/2 routing(config-if)#switchport mode access routing(config-if)#switchport access vlan 172 routing(config)#int gig 1/0/11 routing(config-if)#switchport mode access routing(config-if)#switchport access vlan 10 routing(config-if)#exit routing(config)#int gig 1/0/12 routing(config-if)#switchport mode access routing(config-if)#switchport access vlan 10 routing(config-if)#exit routing(config)#int gig 1/0/5 routing(config-if)#switchport mode access routing(config-if)#switchport access vlan 5 routing(config-if)#exit
4. Configure IP Addresses to VLAN on Switch
| VLAN ID | VLAN Name | VLAN IP Address |
| 172 | vlan-172 | 172.16.0.1 |
| 10 | vlan-10 | 10.0.0.1 |
| 5 | vlan-5 | 5.0.0.1 |
routing(config)#int vlan 172 routing(config-if)#ip address 172.16.0.1 255.255.0.0 routing(config-if)#no shut routing(config-if)#exit routing(config)#int vlan 10 routing(config-if)#ip address 10.0.0.1 255.0.0.0 routing(config-if)#no shut routing(config-if)#exit routing(config)#int vlan 5 routing(config-if)#ip address 5.0.0.1 255.0.0.0 routing(config-if)#no shut routing(config-if)#exit
5. View VLAN Information
The following show commands gives an overview of what VLANs are assigned to which interfaces and the IP Address of VLANs
routing#show vlan br
VLAN Name Status Ports
---- -------------------------------- --------- -------------------------------
1 default active Gig1/0/3, Gig1/0/4, Gig1/0/6, Gig1/0/7
Gig1/0/8, Gig1/0/9, Gig1/0/10, Gig1/0/13
Gig1/0/14, Gig1/0/15, Gig1/0/16, Gig1/0/17
Gig1/0/18, Gig1/0/19, Gig1/0/20, Gig1/0/21
Gig1/0/22, Gig1/0/23, Gig1/0/24, Gig1/1/1
Gig1/1/2, Gig1/1/3, Gig1/1/4
5 vlan-5 active Gig1/0/5
10 vlan-10 active Gig1/0/11, Gig1/0/12
172 vlan-172 active Gig1/0/1, Gig1/0/2
1002 fddi-default active
1003 token-ring-default active
1004 fddinet-default active
1005 trnet-default active
routing#show ip int br
Interface IP-Address OK? Method Status Protocol
GigabitEthernet1/0/1 unassigned YES NVRAM up up
GigabitEthernet1/0/2 unassigned YES NVRAM up up
............
...........
GigabitEthernet1/1/3 unassigned YES NVRAM down down
GigabitEthernet1/1/4 unassigned YES NVRAM down down
Vlan1 unassigned YES NVRAM administratively down down
Vlan5 5.0.0.1 YES manual up up
Vlan10 10.0.0.1 YES manual up up
Vlan172 172.16.0.1 YES manual up up
6. Enabling Routing
Routing might be already enabled. It doesn't hurt to enable one more time.
routing#conf t routing(config)#ip routing routing(config)#exit
In the show command, if Connected Network information is shown, it means routing is enabled.
routing#show ip route
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is not set
C 5.0.0.0/8 is directly connected, Vlan5
C 10.0.0.0/8 is directly connected, Vlan10
C 172.16.0.0/16 is directly connected, Vlan172
7. Validation
Issue ping from any Laptop to any Laptop, it will be success.
 |
| Successful ping from Inside2-1 to Outside |
 |
| Successful ping from Outside to Inside1-1 |
8. Alternate Topology
If there is no multilayer switch and we use Router, our topology has to be like this. We will not be using VLANs. All the laptops that are earlier connected to same VLAN, will be connected to a hub here.
 |